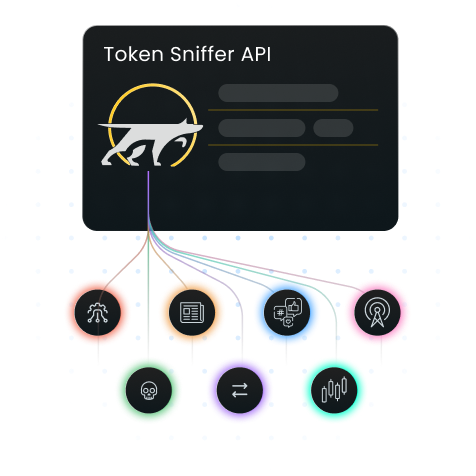
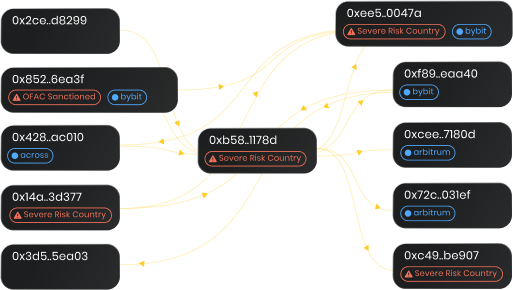
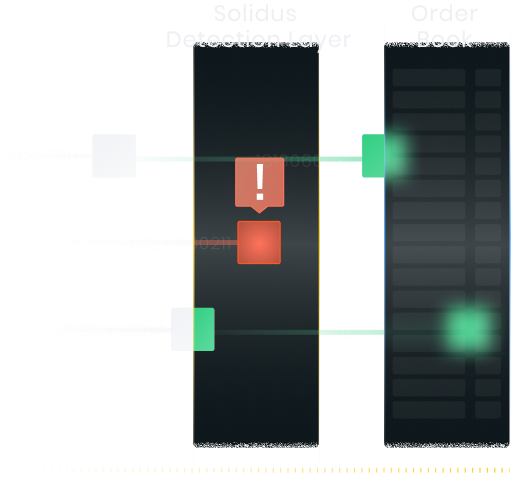
Token Monitoring
Monitor token-level risks, smart contracts scams, liquidity profiles, and distribution patterns, detecting rug pulls, honeypots, and token-level embedded risks to protect investors and maintain platform integrity
Get a Demo
$16T
Daily volume monitored
46,132,395
Tokens monitored
5,728,567
Scams detected






.svg)